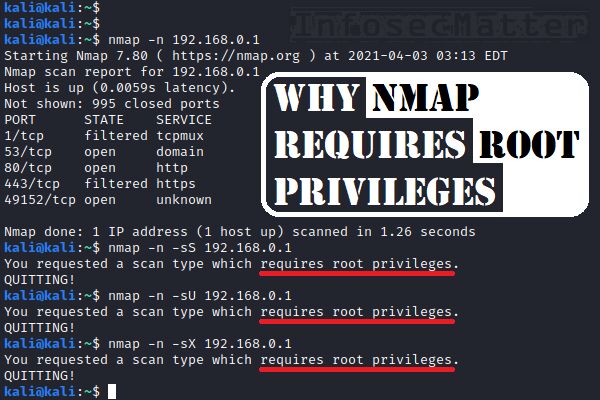
Nmap Network Scanning: The Official Nmap Project Guide to Network Discovery and Security Scanning: 8601404706585: Computer Science Books @ Amazon.com

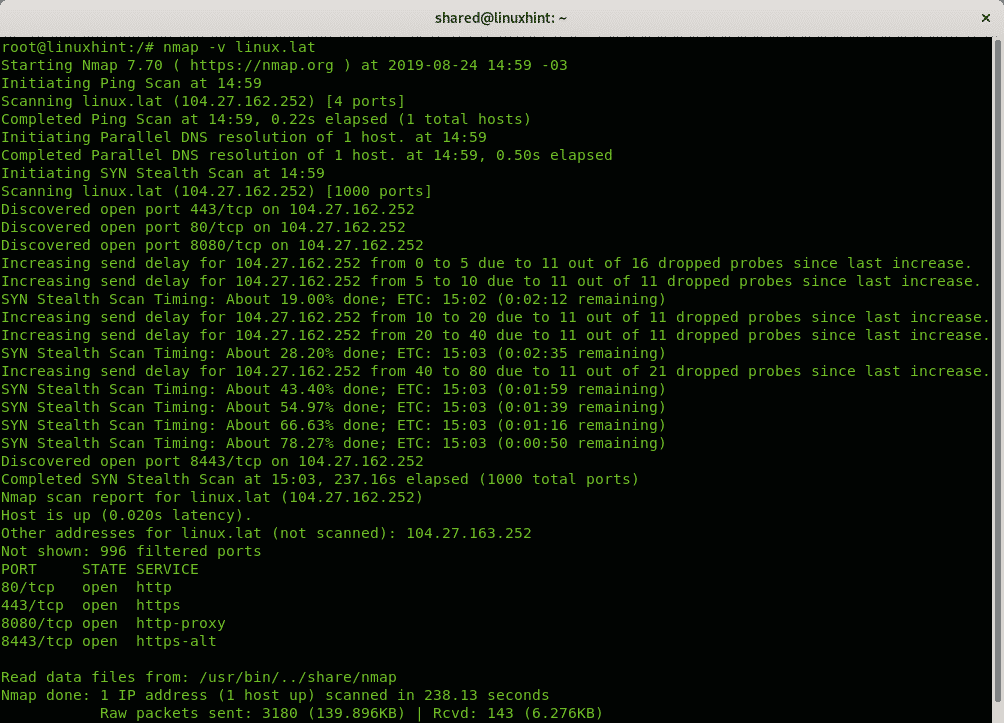
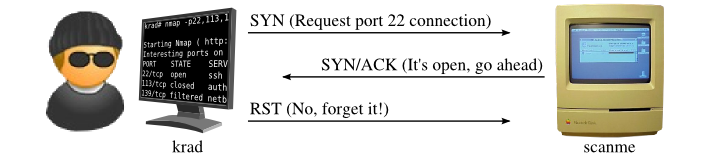
NMAP – How to run an NMAP -sS SYN Stealth Scan on Windows 7 – The Visual Guide | University of South Wales: Cyber University of the year: Three years running: 2019, 2020, 2021